What is Qehu Ransomware?
Qehu Ransomware is a dangerous malware that is designed to encrypt files on a victim’s computer and demand a ransom in exchange for the decryption key. It typically infects computers through malicious email attachments, fake software updates, or compromised websites. Once installed, Qehu Ransomware adds the “.qehu” extension to encrypted files, making them inaccessible to the user.
The ransomware uses strong encryption algorithms such as AES or RSA to lock the files, making it nearly impossible to decrypt them without the decryption key. A ransom note is usually created by Qehu Ransomware and placed in various folders on the infected computer, instructing the victim on how to pay the ransom and receive the decryption key. Unfortunately, there are currently no decryption tools available for .qehu files, making it crucial for users to regularly back up their important data to prevent data loss in case of a ransomware attack.
Ransom note:
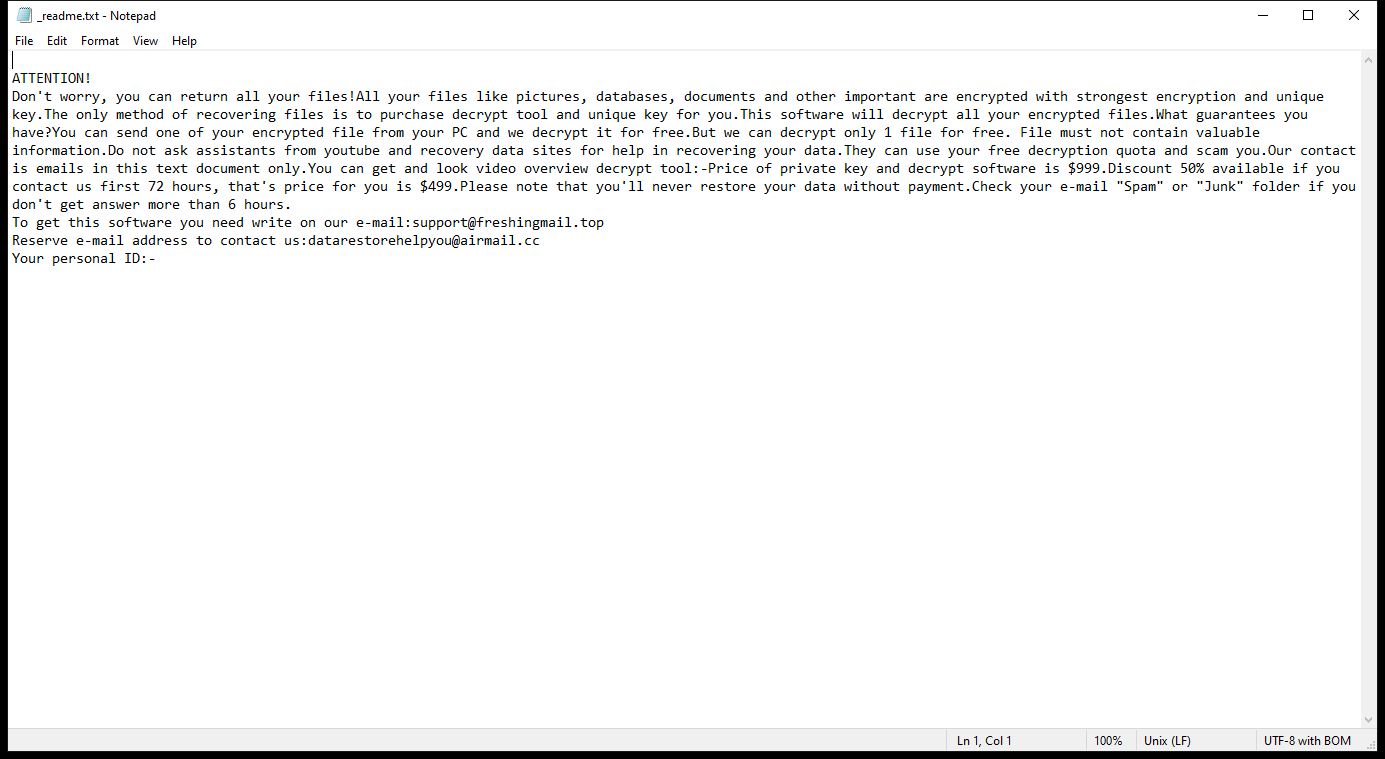
_readme.txt contents:
ATTENTION!
Don’t worry, you can return all your files!All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.The only method of recovering files is to purchase decrypt tool and unique key for you.This software will decrypt all your encrypted files.What guarantees you have?You can send one of your encrypted file from your PC and we decrypt it for free.But we can decrypt only 1 file for free. File must not contain valuable information.Do not ask assistants from youtube and recovery data sites for help in recovering your data.They can use your free decryption quota and scam you.Our contact is emails in this text document only.You can get and look video overview decrypt tool:-Price of private key and decrypt software is $999.Discount 50% available if you contact us first 72 hours, that’s price for you is $499.Please note that you’ll never restore your data without payment.Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
To get this software you need write on our e-mail:support@freshingmail.top
Reserve e-mail address to contact us:datarestorehelpyou@airmail.cc
Your personal ID:-
How Ransomwares Like Qehu Ransomware Ends Up on Users’ Computers:
Ransomware employs various methods to infect computers, exploiting vulnerabilities in both software and human behavior. One common tactic involves malicious email attachments or links, where unsuspecting users inadvertently download and execute the ransomware payload. Additionally, attackers may exploit software vulnerabilities, exploiting security flaws in outdated systems or applications to gain unauthorized access. Another avenue is through malicious websites or ads, which can silently install ransomware when visited. Furthermore, ransomware can spread through networked devices, leveraging weak passwords or unsecured connections to infiltrate entire systems.
- Remove Qehu Ransomware Automatically
- Back up Your Encrypted Files
- Decrypt .qehu Files
- Restore .qehu Files With File Recovery Tools
- Recover Encrypted Files From Shadow Copies
- How to Protect Your PC From Malware and Prevent Ransomware Infections In the Future
Remove Qehu Ransomware
First, we advise you to scan your computer with an antivirus to find and remove all remaining instances of Qehu Ransomware.
Other anti-malware software that may be able to get rid of Qehu Ransomware:
Norton (Windows, macOS, iOS, Android) The link may not work correctly in some countries.
Malwarebytes (Windows)
Back up Your Encrypted Files:
We advise you to create a copy of the encrypted files and put it away. That might help you if free ransomware decryptor becomes available in the future, or if you decide to pay and get the decryptor but something goes wrong and files get irreparably damaged in the process of decryption.
Decrypt .qehu Files:
Most ransomware use very complex encryption methods. Only the creators have the special key needed to unlock the files. Without this key, it’s impossible to get the data back. Usually, the hackers keep these keys on their own servers, not on the infected computers. Some ransomware is so well-made that it’s almost impossible to recover files without the hackers’ help. But some are not so good and have mistakes, like using the same key for everyone or keeping keys on the infected computer. That’s why it’s a good idea to look for tools to unlock your files if you get hit by ransomware. You can use NoMoreRansom site to find if a specific decryption tool for Qehu Ransomware exists.
Restore .qehu Files With File Recovery Tools:
Screenshot:
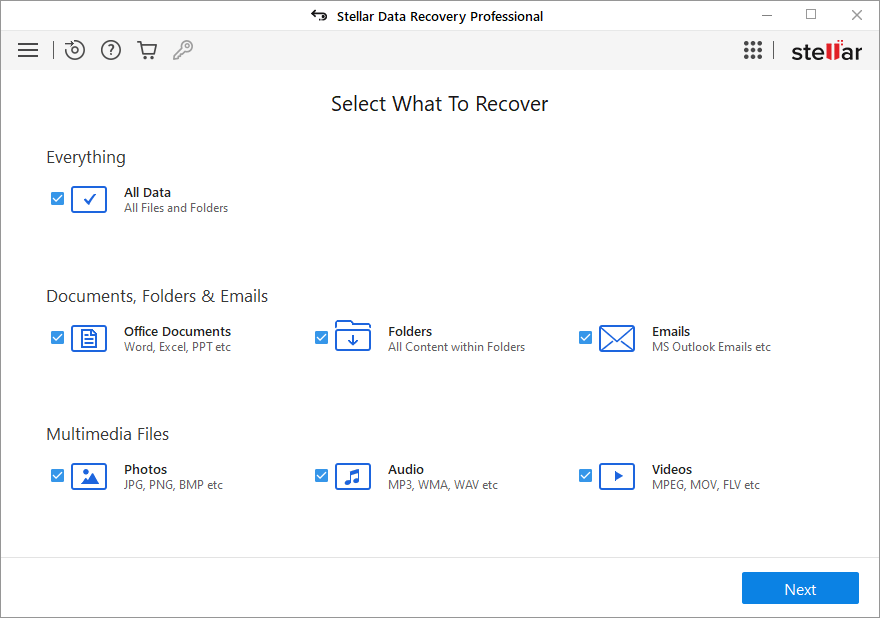
About Stellar Data Recovery
- Retrieves data from formatted, encrypted, or corrupted drives.
- Free trial version allows user to scan, preview and download up to 1GB of data.
- Supports Windows 11, 10, 8 and 7. A Mac variant is also available.
Recover Encrypted Files From Shadow Copies:
Shadow Explorer is a free tool designed to access Shadow Volume Copies in Windows systems. It allows users to retrieve previous versions of files and folders stored in these shadow copies. By selecting a specific disk and date, users may be able to recover lost or overwritten data. Download and install the latest version of Shadow Explorer, or opt for the portable version.
- Launch Shadow Explorer.
- On the top left part of the window pick a disk (C:\, D:\, etc.) and a date when a snapshot of files was captured.
- To retrieve file or a folder, right-click on it and select Export.
- Select the destination where you want to store the files
How to Protect Your PC From Malware and Prevent Ransomware Infections In the Future:
- Keep software updated: Regularly update your operating system, antivirus software, and other applications to patch security vulnerabilities.
- Use antivirus and anti-malware software: Install reputable antivirus and anti-malware programs to detect and remove ransomware threats.
- Enable firewall: Activate and properly configure a firewall to monitor and block suspicious network traffic.
- Backup data regularly: Create and maintain regular backups of important files and data on separate storage devices or cloud services to mitigate the impact of a ransomware attack.
- Exercise caution with email: Be cautious when opening email attachments or clicking on links, especially from unknown or suspicious senders.
- Stay informed: Stay up-to-date on the latest ransomware threats, tactics, and prevention strategies to adapt your defenses accordingly.
