What is Kcvp ransomware?
Kcvp is a novel strain of STOP/Djvu ransomware. More than a thousand strains exist, and most of them are nearly identical to each other. After encrypting the files, all STOP/Djvu strains add a four-letter extension to their names; in this case, .kcvp file extension. The strains are named after these extensions, as it is the easiest way to distinguish them. Although even these names are often similar; for example Tcvp is an another recent version of STOP/Djvu.
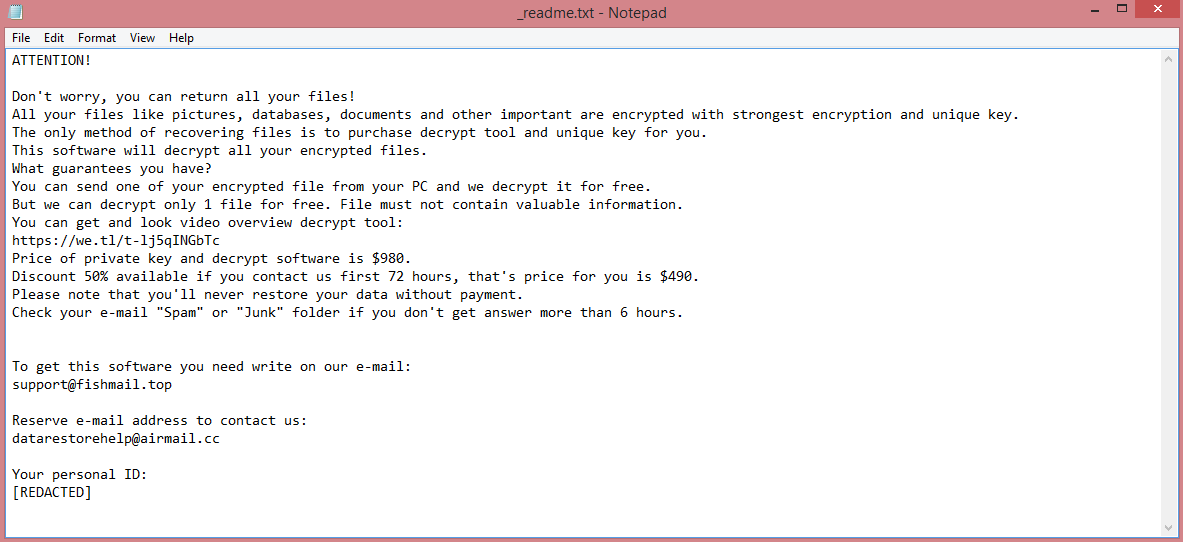
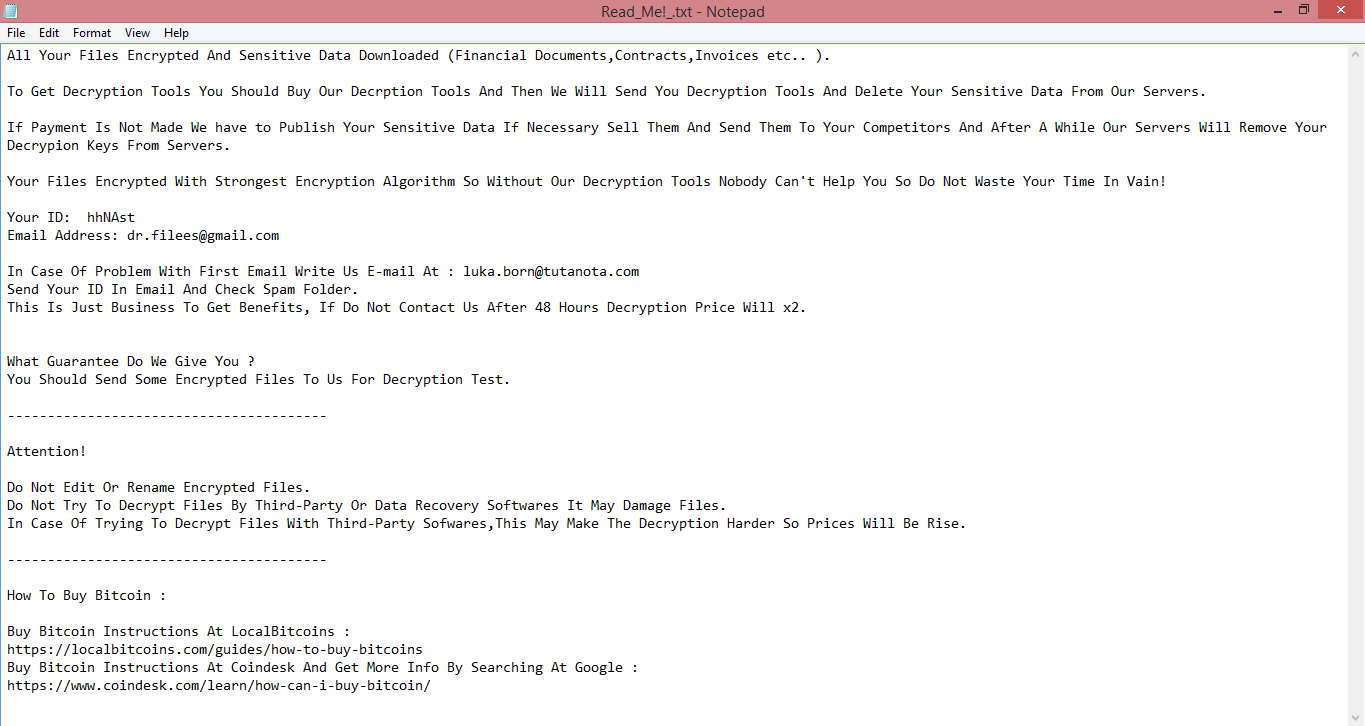
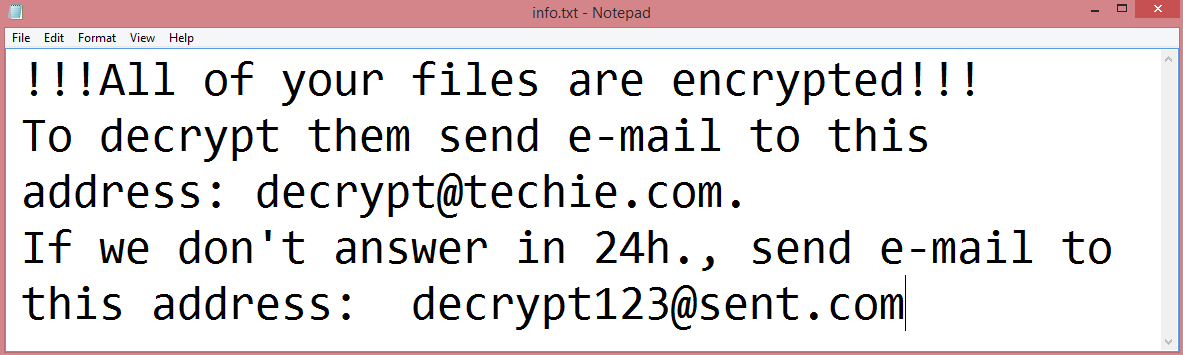
After this, the ransomware creates a ransom note. The note, named “_readme.txt”, always contains the same text, though the hackers’ contact information might differ. The virus demands $980 to decrypt the files, and offers a 50% discount to those who pay within 3 days as a manipulative trick. Full text of the note is available on the image above.
Almost a thousand dollars is quite a lot of money. It’s likely that you don’t want to pay that much to restore your files. With that in mind, we’ve prepared a guide explaining alternative ways to remove Kcvp ransomware and decrypt .kcvp files, those that don’t involve paying the hackers.
![Vohuk ransom note:
[~] Vohuk Ransomware V1.3
>>> What's happened?
ALL YOUR FILES ARE STOLEN AND ENCRYPTED.
To recovery your data and not to allow data leakage, it is possible only through purchase of a private key from us.
>>> What guarantees?
We are not a politically motivated group and we do not need anything other than your money.
Before paying you can send us up to 2 files for free decryption.
The total size of files must be less than 2MB(non archived).
files should not contain valuable information. (databases, backups, large excel sheets, etc.)
>>> CONTACT US:
Please write an email to both: payordiebaby@tutanota.com & payordiebaby69@msgsafe.io
Write this Unique-ID in the title of your message: [REDACTED]
>>> ATTENTION!
Do not delete or rename or modify encrypted files.
Do not try to decrypt using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price(they add their fee to our).
We use strong encryption, nobody can restore your files except us.
The price depends on how fast you contact with us.
remember to hurry up, as your email address may not be available for very long.
All your stolen data will be loaded into cybercriminal forums/blogs if you do not pay ransom.
If you do not pay the ransom we will attack your company repeatedly again.
This is the end of the note. Below you will find a guide explaining how to remove Vohuk ransomware.](https://www.computips.org/wp-content/uploads/2022/11/how-to-remove-vohuk-ransomware.png)