![DATAF LOCKER ransom note:
----------- [ Hello! ] ------------->
****BY DATAF L**OCKER****
What happend?
----------------------------------------------
Your computers and servers are encrypted, backups are deleted from your network and copied. We use strong
encryption algorithms, so you cannot decrypt your data.
But you can restore everything by purchasing a special program from us - a universal decoder. This program will
restore your entire network.
Follow our instructions below and you will recover all your data.
If you continue to ignore this for a long time, we will start reporting the hack to mainstream media and posting
your data to the dark web.
What guarantees?
----------------------------------------------
We value our reputation. If we do not do our work and liabilities, nobody will pay us. This is not in our
interests.
All our decryption software is perfectly tested and will decrypt your data. We will also provide support in case
of problems.
We guarantee to decrypt one file for free. Go to the site and contact us.
How to contact us?
----------------------------------------------
Using TOR Browser ( https://www.torproject.org/download/ ):
tor chat: http://tiurksxrhrefu6uzunlkpugr5rzejfeptxr4pauvsyzp4mlzuqmiatad.onion/feDJtT2hZC5X2ICH2Qq8
login: [REDACTED]
Password: [REDACTED]
----------------------------------------------
!!! DANGER !!!
DO NOT MODIFY or try to RECOVER any files yourself. We WILL NOT be able to RESTORE them.
!!! DANGER !!
This is the end of the note. Below you will find a guide explaining how to remove DATAF LOCKER ransomware.](https://www.computips.org/wp-content/uploads/2022/12/how-to-remove-dataf-locker-ransomware.png)
What is DATAF LOCKER ransomware?
DATAF LOCKER is a malevolent program classified as ransomware. It performs a specific set of actions with the aim of holding the victim’s files for ransom (hence, ransomware).
The first, and the most essential, step that any ransomware program performs is file encryption. By utilizing cryptographic algorithms, these viruses encrypt all user data on the computer: pictures, videos, text documents, etc. These files are “locked” in the sense that it is not possible to view or edit them. To return them to their original state, they must be decrypted first.
During the second step, the program renames the files that were encrypted. Although not necessary, most ransomware programs do it to signal that something is wrong to the victim. In DATAF LOCKER’s case, the affected files are given .dataf file extension.
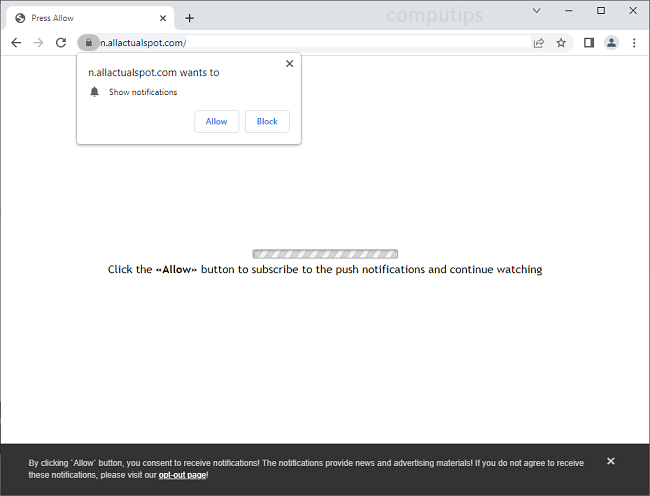
The last step is the creation of a ransom note, which is essential as well. Since any ransomware program exists to generate money, it needs to communicate its demands to the victim. DATAF’s ransom note can be read on the image above.
Whether to pay the hacker or not is a personal decision, but paying is associated with many risks and generally not recommended. Our guide presents an alternative: a way to remove DATAF LOCKER ransomware and decrypt .dataf files without having to contact the criminal at all.
![Bazek ransom note:
All your important files have been encrypted with AES256 by the Bazek Ransomware!
Reach out to me via e-mail at bazeksupport@onionmail.org to get your files decrypted
We will delete your decryption key if you do not contact us withing 48 Hours and your files are gone forever!
Personal identification code: [REDACTED]
This is the end of the note. Below you will find a guide explaining how to remove Bazek ransomware.](https://www.computips.org/wp-content/uploads/2022/12/how-to-remove-bazek-ransomware.png)

![RansomBoggs ransom note:
Dear human life form!
This is James P. Sullivan, an employee of Monsters, Inc.
Recently our company has again expecienced great financial problems and we require some cash to move on with our
electronic crap.
So we are relying on you in these hard times and are crying for help.
I am extremely sorry for the inconvenience but I am currently encrypting your documents using AES-128.
This key is encrypted using RSA public key and saved to aes.bin file:
[ C:\Users\[REDACTED]\Desktop\aes.bin ]
Please, DO NOT WORRY! I have a decrypting functionality too.
Just don't delete aes.bin, please. You will need it!
==================================================================================
You just need to contact me:
m0nsters-inc@proton.me
https://t.me/m0nsters_inc
TOX 76F64AF81368A06D514A98C129F56EF09950A 8C7DF19BB1B839C996436DCD36A6F27C4DF00A6
==================================================================================
This is the end of the note. Below you will find a guide explaining how to remove RansomBoggs ransomware.](https://www.computips.org/wp-content/uploads/2022/11/how-to-remove-ransomboggs-ransomware.png)