What is Rapax Ransomware?
Rapax Ransomware is a type of malicious software that encrypts files on a victim’s computer and demands a ransom in exchange for the decryption key. It typically infects computers through phishing emails, malicious websites, or software vulnerabilities. Once a computer is infected, Rapax Ransomware adds a specific file extension to all encrypted files, such as .rapax, making them inaccessible to the user.
The ransomware uses strong encryption algorithms, such as AES or RSA, to lock the files and prevent users from accessing them without the decryption key. A ransom note is usually created by Rapax Ransomware and left on the victim’s desktop or in folders containing encrypted files, providing instructions on how to pay the ransom and receive the decryption key. While there may be some decryption tools available for certain ransomware variants, there is currently no known decryption tool for Rapax Ransomware. If you have been infected with Rapax Ransomware, it is recommended to regularly backup your files, avoid paying the ransom as it does not guarantee file recovery, and seek assistance from cybersecurity professionals for further guidance on how to recover your encrypted files.
Ransom note:
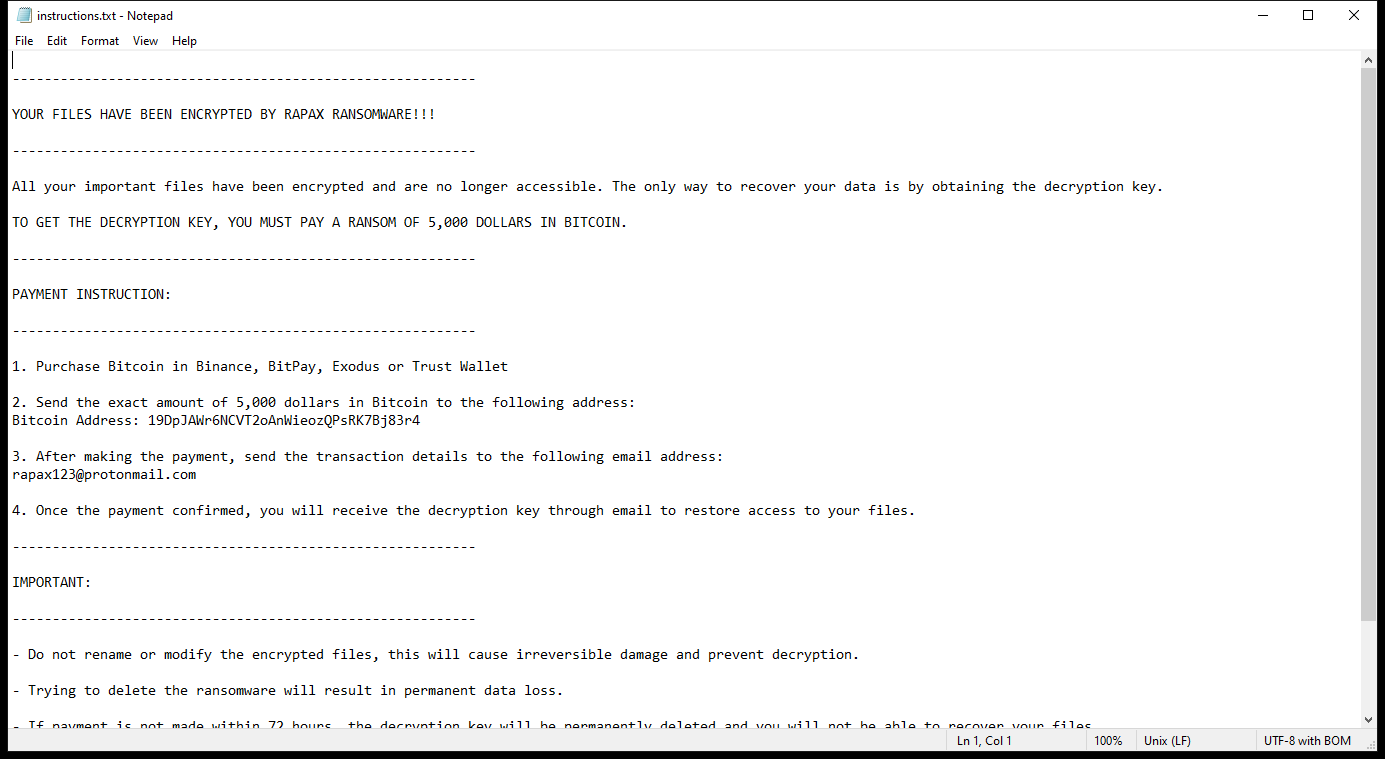
instructions.txt contents:
———————————————————-
YOUR FILES HAVE BEEN ENCRYPTED BY RAPAX RANSOMWARE!!!
———————————————————-
All your important files have been encrypted and are no longer accessible. The only way to recover your data is by obtaining the decryption key.
TO GET THE DECRYPTION KEY, YOU MUST PAY A RANSOM OF 5,000 DOLLARS IN BITCOIN.
———————————————————-
PAYMENT INSTRUCTION:
———————————————————-
1. Purchase Bitcoin in Binance, BitPay, Exodus or Trust Wallet
2. Send the exact amount of 5,000 dollars in Bitcoin to the following address:
Bitcoin Address: 19DpJAWr6NCVT2oAnWieozQPsRK7Bj83r4
3. After making the payment, send the transaction details to the following email address:
rapax123@protonmail.com
4. Once the payment confirmed, you will receive the decryption key through email to restore access to your files.
———————————————————-
IMPORTANT:
———————————————————-
– Do not rename or modify the encrypted files, this will cause irreversible damage and prevent decryption.
– Trying to delete the ransomware will result in permanent data loss.
– If payment is not made within 72 hours, the decryption key will be permanently deleted and you will not be able to recover your files.
ACT NOW TO RECOVER YOUR DATA!!!
– Rapax Ransomware
How Ransomwares Like Rapax Ransomware Ends Up on Users’ Computers:
Ransomware employs various methods to infect computers, exploiting vulnerabilities in both software and human behavior. One common tactic involves malicious email attachments or links, where unsuspecting users inadvertently download and execute the ransomware payload. Additionally, attackers may exploit software vulnerabilities, exploiting security flaws in outdated systems or applications to gain unauthorized access. Another avenue is through malicious websites or ads, which can silently install ransomware when visited. Furthermore, ransomware can spread through networked devices, leveraging weak passwords or unsecured connections to infiltrate entire systems.
- Remove Rapax Ransomware Automatically
- Back up Your Encrypted Files
- Decrypt .rapax Files
- Restore .rapax Files With File Recovery Tools
- Recover Encrypted Files From Shadow Copies
- How to Protect Your PC From Malware and Prevent Ransomware Infections In the Future
Remove Rapax Ransomware
First, we advise you to scan your computer with an antivirus to find and remove all remaining instances of Rapax Ransomware.
Other anti-malware software that may be able to get rid of Rapax Ransomware:
Norton (Windows, macOS, iOS, Android) The link may not work correctly in some countries.
Malwarebytes (Windows)
Back up Your Encrypted Files:
We advise you to create a copy of the encrypted files and put it away. That might help you if free ransomware decryptor becomes available in the future, or if you decide to pay and get the decryptor but something goes wrong and files get irreparably damaged in the process of decryption.
Decrypt .rapax Files:
Most ransomware use very complex encryption methods. Only the creators have the special key needed to unlock the files. Without this key, it’s impossible to get the data back. Usually, the hackers keep these keys on their own servers, not on the infected computers. Some ransomware is so well-made that it’s almost impossible to recover files without the hackers’ help. But some are not so good and have mistakes, like using the same key for everyone or keeping keys on the infected computer. That’s why it’s a good idea to look for tools to unlock your files if you get hit by ransomware. You can use NoMoreRansom site to find if a specific decryption tool for Rapax Ransomware exists.
Restore .rapax Files With File Recovery Tools:
Screenshot:
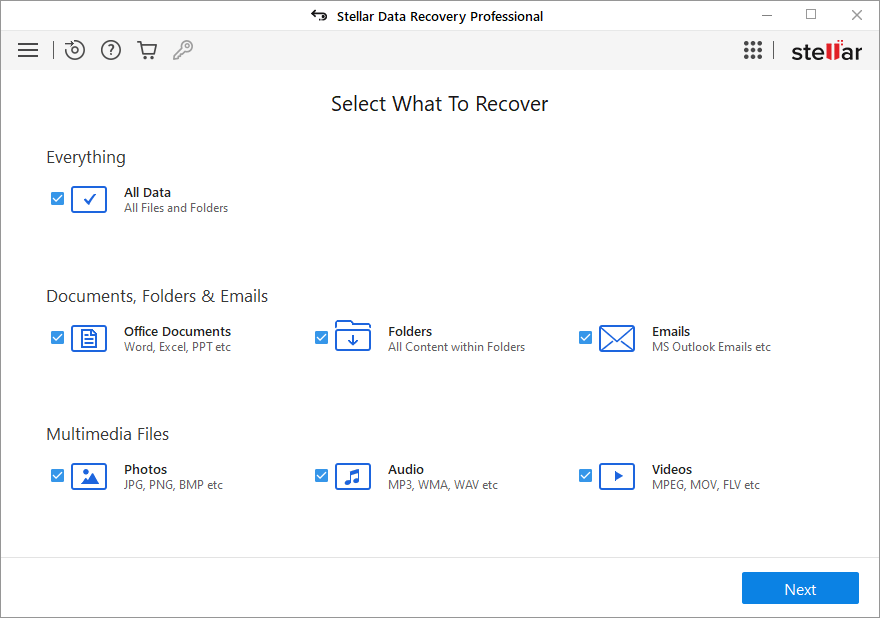
About Stellar Data Recovery
- Retrieves data from formatted, encrypted, or corrupted drives.
- Free trial version allows user to scan, preview and download up to 1GB of data.
- Supports Windows 11, 10, 8 and 7. A Mac variant is also available.
Recover Encrypted Files From Shadow Copies:
Shadow Explorer is a free tool designed to access Shadow Volume Copies in Windows systems. It allows users to retrieve previous versions of files and folders stored in these shadow copies. By selecting a specific disk and date, users may be able to recover lost or overwritten data. Download and install the latest version of Shadow Explorer, or opt for the portable version.
- Launch Shadow Explorer.
- On the top left part of the window pick a disk (C:\, D:\, etc.) and a date when a snapshot of files was captured.
- To retrieve file or a folder, right-click on it and select Export.
- Select the destination where you want to store the files
How to Protect Your PC From Malware and Prevent Ransomware Infections In the Future:
- Keep software updated: Regularly update your operating system, antivirus software, and other applications to patch security vulnerabilities.
- Use antivirus and anti-malware software: Install reputable antivirus and anti-malware programs to detect and remove ransomware threats.
- Enable firewall: Activate and properly configure a firewall to monitor and block suspicious network traffic.
- Backup data regularly: Create and maintain regular backups of important files and data on separate storage devices or cloud services to mitigate the impact of a ransomware attack.
- Exercise caution with email: Be cautious when opening email attachments or clicking on links, especially from unknown or suspicious senders.
- Stay informed: Stay up-to-date on the latest ransomware threats, tactics, and prevention strategies to adapt your defenses accordingly.
